LONDON —
Veracode, a leading global provider of intelligent software security, today released research indicating applications developed by organisations in Europe, Middle East and Africa tend to contain more security flaws than those created by their U.S. counterparts. Across all regions analysed, EMEA also has the highest percentage of ‘high severity’ flaws, meaning they would cause a critical issue for the business if exploited. High numbers of flaws and vulnerabilities in applications correlate with increased levels of risk, which is particularly notable as software supply chain cyberattacks dominate headlines in 2023.
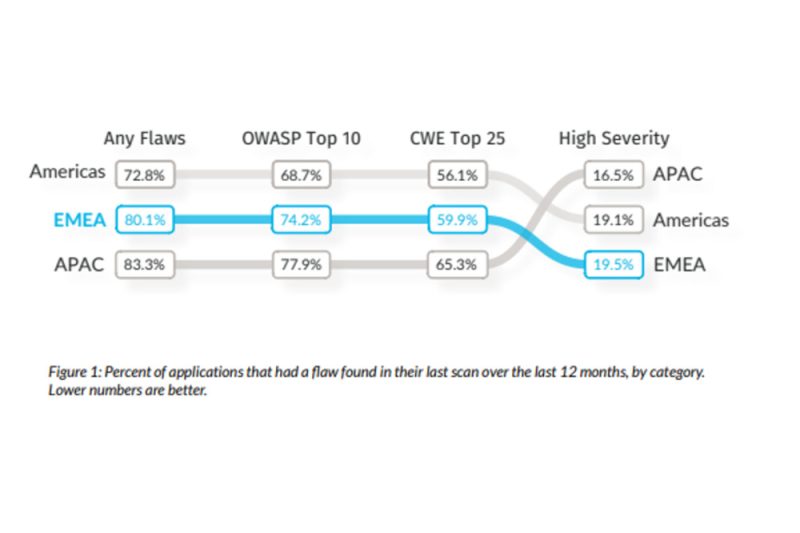
Researchers found that just over 80 percent of applications developed by EMEA organisations had at least one security flaw detected in their most recent scan over the last 12 months, compared to just under 73 percent of U.S. organisations. In addition, the percentage of applications containing ‘high severity’ flaws was the highest of all regions, at almost 20 percent.
“Our data shows that organisations globally are continuing to deploy a worrying number of applications with a high number of flaws in the CWE Top 25,” said Chris Eng, Chief Research Officer at Veracode. “We did, however, identify interesting regional differences, particularly in terms of third-party or open-source code usage and the ways in which vulnerabilities are introduced across the application lifecycle,” he continued.
Analysis of data collected from more than 27 million scans across 750,000 applications helped to produce Veracode’s latest annual report on the State of Software Security. This new report showcases the EMEA-specific findings from those scans and applications, including results from UK, Germany, France, Italy and across the Middle East and Africa.
Numbers alone don’t convey the consequences of hackers exploiting software vulnerabilities. With organisations across EMEA utilising an ever more complex mix of third-party software to deliver their services, the exploitation of a serious vulnerability can impact thousands of victims at once. Earlier this year, a vulnerability affecting printing software tools PaperCut MF and PaperCut NG was actively abused by threat actors. Up to 70,000 organisations in 200 countries became potential victims, and law enforcement reports found threat actors successfully compromised vulnerable entities in the education sector.
Java and Third-party Code Introduce Significant Security Flaws
The research identified notable regional differences in preferred language usage, with Java revealed to be the preferred language for developers in EMEA. Teams using Java were found to remediate flaws at a slower rate than those using .NET or JavaScript, causing many of these flaws to persist or remain undiscovered for significantly longer. Moreover, as over 95 percent of Java applications are comprised of third-party or open-source code, Java usage is a key factor in the higher percentage of vulnerabilities introduced into applications in the region. This highlights the importance of software composition analysis (SCA), which picks up flaws in open-source code, and the research found a higher proportion of flaws reported by SCA in EMEA than in other regions.
As generative AI continues to gain strong traction in software development, the risk of vulnerabilities from external sources increases. A study, presented at Black Hat in 2022, showed vulnerabilities in 40 percent of code that had been written by large language models trained on vast troves of unrefined data, including millions of public GitHub repositories. It is therefore vital organisations leverage SCA tools to find and fix flaws, empowering developers to take advantage of AI without compromising the security of applications.
Applications Become More Vulnerable Over Time
The research also showed new flaws continue to be introduced into EMEA applications at a far higher rate across the entire application lifecycle than in other regions. While EMEA organisations keep updating applications, there was less of a focus on quality. After a five-year timespan, 50 percent of applications in EMEA continue to introduce new flaws, compared to just over 30 percent for the rest of the world. Overall, the baseline chance that a flaw will be introduced in any given month was 27 percent.
As such, EMEA organisations would benefit from paying more attention to the latter portion of the application lifecycle and scanning applications more regularly. They should also prioritise security training for developers, with the research finding completion of 10 interactive security labs reduces the probability of flaw introduction from 27 percent to about 25 percent in any given month.
“This year’s State of Software Security report shines a light on the importance of security across the entire software lifecycle, as well as the urgent need to address risks posed by third-party and AI-generated code,” Eng added. “Whilst across the board globally we are still seeing a concerning volume of vulnerabilities, these figures are higher in EMEA across almost all measurements. Development teams in this region must take the opportunity to automate software security for regular scanning, and carefully consider their use of AI tools, both to increase security and empower developers.”






























